How To View Private Facebook Profiles & Pictures

Facebook’s privacy protection guidelines mean you can only see limited information about a locked or private profile if you are not a mutual Facebook friend with them. So, what are your options if you want to see a private Facebook profile or pictures posted by a private account? In this article, we will discuss some of the options and legalities in this article.
There are a lot of third-party apps and websites that claim to show content posted from a private Facebook profile. Unfortunately, many of these don’t work while a lot of them are scams trying to access your personal information or get money from you. In these situations, it is always a “Buyer Beware” scenario.
To get started, let’s first review the types of security options Facebook offers and how it works.
Facebook’s Privacy
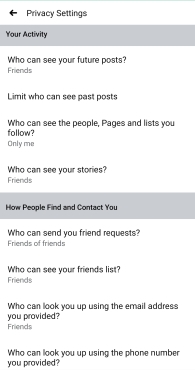
Facebook offers a four-tier system where you can set your preferred profile privacy level:
- If you’re friends with someone, you can generally see everything they have online, with the exception of posts that they have specifically chosen to exclude you from seeing.
- If you aren’t friends with someone, but their profile is public, you can see most of what they have online.
- If you aren’t friends with someone and their profile is private, you won’t be able to see anything other than their existence on Facebook and their main profile photo.
- Finally, if you have blocked someone on Facebook, they won’t be able to see anything at all (or the fact that you have a Facebook account) regardless of their other privacy settings.

Facebook Privacy Explained
Assuming the profile you’d like to review is private, you won’t be able to see much. If that person blocked you, regardless of their privacy settings, you can’t find them on Facebook at all. Although you may see their messages in Messenger accompanied by a static “User” profile picture.
Despite these privacy settings, there used to be a technical weakness in the Facebook site that would allow you to get at least some of the information you’re interested in. Previously, you could manipulate a Facebook profile URL with the person’s name to see some of their timeline and images, though this exploit doesn’t work anymore.
Other similar exploits and cracks in Facebook’s privacy and security settings, like the ability to use a Facebook graph URL to access private images or the option to use third-party tools to circumvent Facebook’s own privacy locks, don’t work either.
Facebook has come under scrutiny in recent years for its privacy missteps, and as a result, they’ve enhanced their security measures to ensure your Facebook account is not easily hacked.
In the past, Meta would allow third-party to access private content. However, after coming under scrutiny, the company focuses more on keeping your information private. As a result, there are no technical workarounds for gaining access to a private profile.
This also means that sites and tools claiming to get you secret access to Facebook profile information are likely to break, if they aren’t already broken, and might be a scam on their own.
So, is it hopeless?
Actually, no. Where software engineering has successfully raised privacy walls, social engineering can get you past them. There are a few different approaches that you can take, and in this article, we’ll show you how to work with each one of them.
The Brute Force Method
The simplest and quickest way to gain access to someone’s profile information is probably to pay a data broker for it. This can be a private eye, an online investigative service, or a skilled hacker utilizing data bought on the Dark Web.

Not every single profile is available from this route, but many are. The downside? There are several. One is that you’re working with someone who may be breaking the law and depending on where you’re located, you may be breaking the law as well. If you’re trying to gain access to a Facebook profile as evidence in a legal matter, you shouldn’t use this method.
Another downside is that nobody does that kind of work for fun. You’re going to pay for the information you want. Often this is only a snapshot of the profile and does not grant you permanent access to the account’s activity.
Finally, even if you pay, you aren’t guaranteed to get the kind of results you want. That person’s profile may be out-of-date or contain information that’s not relevant to your search.
The Charm Offensive
Depending on your relationship with the person in question, you can gain access by sending a friend request. Although this may seem obvious, it’s the most effective way of seeing a private profile.

If you suspect that won’t work (either because they don’t know you or because they just don’t consider you a friend), what can you do? There are a few options outside of becoming Facebook friends.
If you have profile information on the individual you can search out any groups or close friends of this person for more information.
You want to get involved with that person’s groups and close friends because you can find yourself in legitimate interactions with that person. It’s in those interactions that you can familiarize the subject person with your online persona, present yourself as a good and worthy Facebook friend, and eventually wind up on their Friends list. Here are some dos and don’ts.
Do:
- Like, Ha-Ha, or Love their posts/pictures/comments, as appropriate.
- Make meaningful responses to their comments.
- Respond to other people in the group or other comments and posts by a third party person so as to present the image of someone who just happens to be there.
- Post friendly responses and engage with their friends.
- Post about your own issues and ideas regardless of the subject person’s interests.
Don’t:
- Start reacting to or commenting on everything they say or do. Let a good 2/3 or 3/4 of it go by without comment.
- Go back into the past and like old stuff – that makes you look like a deliberate stalker.
- Comment constantly so that they feel like you’re suddenly an interloper on their feed.
- Spam their friends list trying to friend everyone.
- Get into conflicts with the subject person.
With care and patience, you can turn yourself from a stranger into a new friend of the subject person – and they’ll be the one to send you the friend request.
The Long Game
If you can’t hire a broker and you’ve been blocked deliberately so a charm offensive isn’t going to work, what’s left? Trickery and deception, of course.
Security experts are unanimous: the weakest link in any security system is the human element. It’s true with theft-prevention systems, it’s true with password cracking, and it’s true with Facebook profile security. The manipulation of this human element is the basis for the technique known as social engineering.
Strategy Based On Research Paper
A 2011 research paper by social scientists at the University of British Columbia reported an experiment in sending friend requests to complete strangers.
As one might expect, sending a friend request to someone with whom the sender had no mutual friends had only a 20% success rate. However, if the friend request came from someone with mutual friends to the recipient – even just one – the odds of a friend request jumped dramatically.
Requests with one mutual friend had an almost 50% success rate, and each additional friend increased the odds of success.
At eleven mutual friends, the chance of success was about 80%. We have a tendency to assume that anyone with whom we have mutual friends must be in our social network somehow – we’re just misplacing them mentally. And so, we hit Accept.
This research shows us the way to help you get access to someone’s profile. We should note at this point that this is not an honest, forthright, or virtuous approach to connecting to someone on Facebook.
If a person isn’t willing to accept your direct friend request, then it is probably unethical for you to use deceptive means to trick them into accepting a friend request from a different person. That said, if you are a sociology student, or otherwise legally interested in the boundaries of social engineering, the tips here might help you write a very successful thesis paper.
The basic idea is simple: you want your fake or cover profile to have multiple mutual friends with your target person. Here’s how you do it.
How to Become a Fake Friend
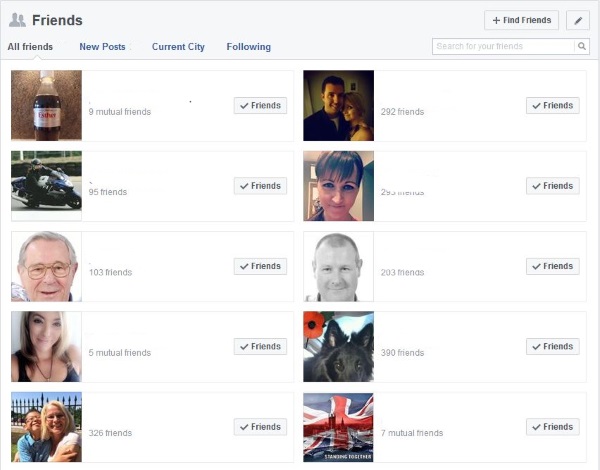
To create a fake profile, you won’t need an email address or phone number, but you might need a little information about the person you’re trying to connect with. Having information about their current friends list is ideal. For most people, even a private profile will show information such as friends, current employer, education, and interests.
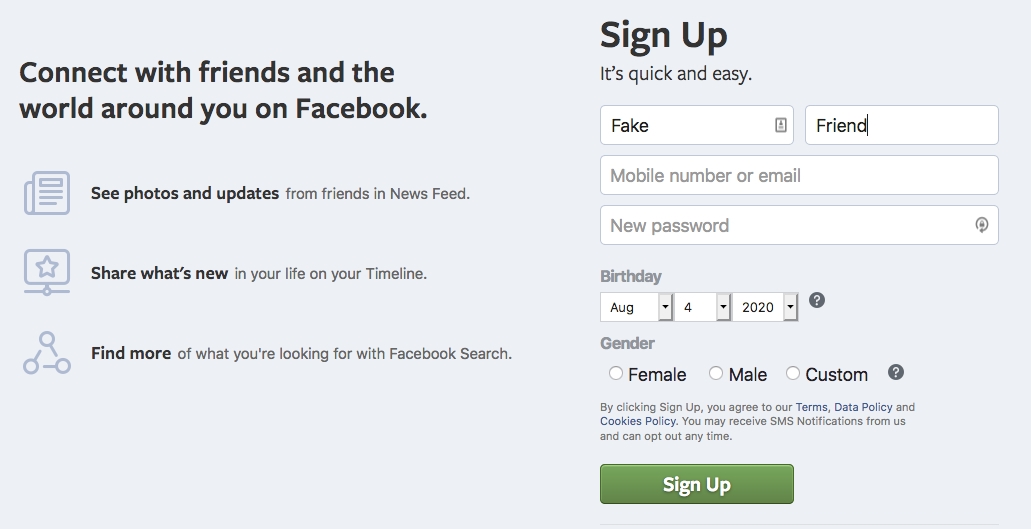
Creating a profile that is interesting to the user or could be a past acquaintance will increase your likelihood of being accepted as a friend. It’s recommended that you use a profile picture of a non-copyrighted image rather than a person as that could get you into legal trouble.
You may need to use LinkedIn and Google to find additional information on the person. Privacy is tough to manage, and unless they are seriously paranoid about their online privacy, you should be able to find out who at least some of their friends are.
Building your fake Facebook profile will require a little work to appear more realistic. Adding posts, friends, and pictures is ideal. If you have mutual contacts on your friends list this will help as well.

Connecting with Mutual Friends
To increase the likelihood of approval you will have to have mutual friends. This requires sending friend requests to mutual acquaintances. This might mean sending requests to friends of friends.
A lot of your initial requests might get ignored or blocked, but many people just semi-automatically approve any friend requests without much research. This is another way you can make your profile look more legitimate and therefore gain access to the private profile.
The next step is to send a friend request to the profile in question and hope for the best.
Endgame
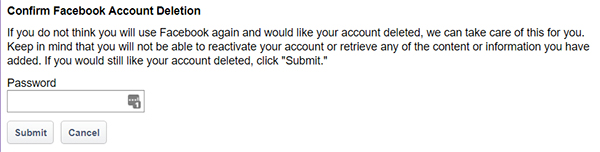
Now that you’re friends, do you want to continue the deception and have permanent access to the profile? Or do you want to record the information you wanted, delete the account, and head for the hills? That’s up to you.
Be aware that the longer you keep the fake account going, the more likely it is that the person will know that it’s a fake account.
A Very Serious Note!
To be very clear: neither myself nor TechJunkie suggests using social engineering to manipulate and trick someone into adding you and approving your friend request on Facebook, Instagram, or any other social network online.
This is not just dangerous and time-consuming but also possibly illegal, depending on where you reside and what laws protect your internet and identity use in your area. Even so, using the guide above essentially counts as catfishing, which brings up its fair share of legal and ethical quandaries.
Pretending to be someone you’re not, even if you don’t break a law, can cause irreparable harm to the feelings, emotions, and mental health of your target, and you should keep the social risk in mind when participating in an act like this.
Whatever your motivation, it’s best to just “get in and get out,” as the saying goes, deleting the account when you’ve found the piece of information you need. The longer you keep up a false account, the more likely someone will realize you aren’t really who you say you are.
Can a Lawyer Subpoena Facebook?
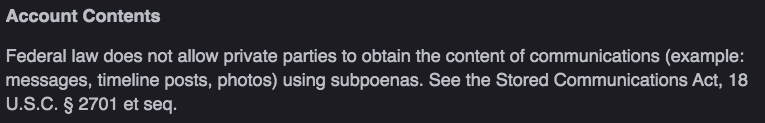
Involving a lawyer to access the information you need, whether it be for divorce or some other civil case can be tricky. Facebook is protected by federal law, they do not have to cooperate with a Subpoena in civil matters.
This means you may get some very basic information about a private Facebook account, but you won’t get messages, photos, or content from posts, according to Facebook.
Facebook does work with law enforcement agencies and will provide information as they must adhere to warrants and court orders. The company does charge the agency for this data unless it involves the safety of a child.
Frequently Asked Questions
A. Unfortunately, no. You will have to log into a Facebook account to see any account details, pictures, or posts. Even if you perform a search using Google, the webpage will redirect you to log in.
A. No. While there are plenty of websites and applications that offer this service, they rarely pan out to be truthful. If you visit someone’s profile frequently, there’s no notification that goes to the owner.
This means you can view a friend’s profile as you’d like, but if you comment, like, or interact with the person’s account, they’ll know you’re looking (especially if it’s a much older post you would’ve had to scroll to see).
A. Unfortunately, you can’t see photos of a private account on Facebook unless you’re friends with them.
A. No, there is no way you can see the content of someone’s Facebook profile without being friends if they have a private account. However, if their profile is public, you can see the content of that person’s Facebook profile without being friends.













10 thoughts on “How To View Private Facebook Profiles & Pictures”