How to Skip the Windows 10 Login Screen and Log Into Your User Account Automatically

We have more passwords than ever before – passwords for email, passwords for Facebook, and Instagram Snapchat. You’ve got a password for your Netflix account and a password for your bank account. You probably have a password to log on at work, passwords for all your different online accounts, a keycode to get into your apartment building, then you walk up to your computer, turn it on, and… yep, Windows 10 wants a password too.
Sometimes you need those passwords – there are bad actors out there who will happily steal your personal information. But for many Windows home users, particularly people who are the only person with physical access to the machine, having a password to get into Windows is a layer of security that wasn’t requested and isn’t needed.
Starting with the Windows 8 release and continuing on through Windows 10, Microsoft has set up the operating system such that users must type their password to log into their account after every reboot and after every account switch. The Windows 10 password login screen will appear by default for any user account with which a password is associated.

If your home machine is physically secure – that is, nobody else has physical access to it – and if there’s not critical personal data (such as banking information, work account login information), then configuring your system to bypass the password every time you log on could be a reasonable trade-off for you.
Removing the login screen from your computer and giving yourself instant login access does a lot to speed up Windows 10, and in this article, we’ll look at how to do just that. We’re also going to look at some security tools you can use to make your computer more secure without adding a password.
How to Bypass or Disable the Windows 10 Login Screen
Before we start, a very important note – we’re not going to actually remove the password from your account, instead, we’re going to configuring Windows 10 to not request the password at all these user switches and warm reboots.
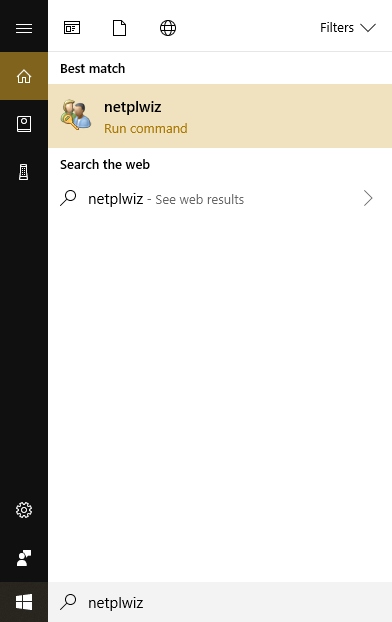
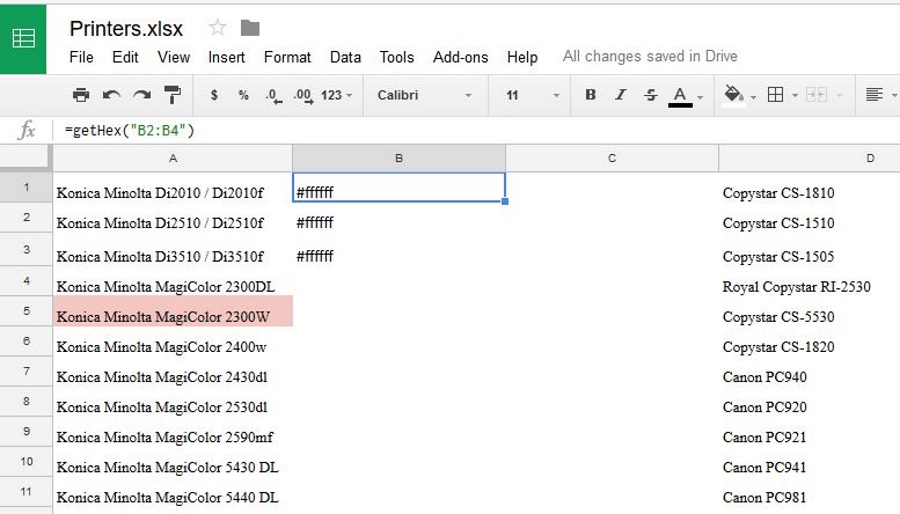
- In the search box next to the Windows logo on your desktop, type netplwiz and hit enter.

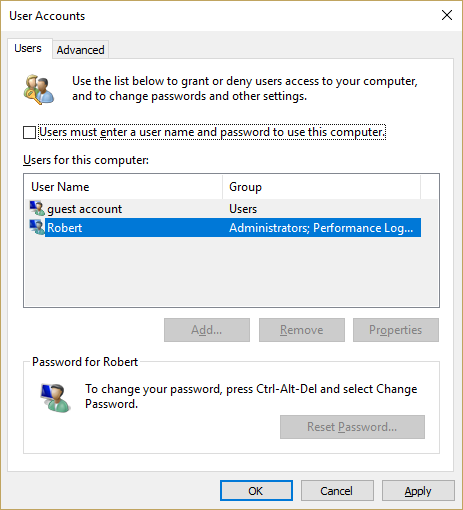
- Click on your user account to select it and uncheck the box labeled Users must enter a user name and password to use this computer. Click OK.

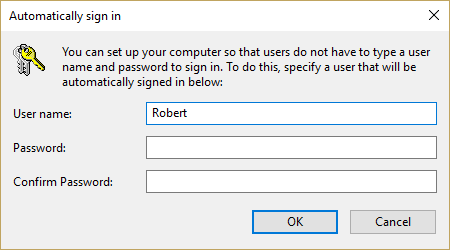
- When asked, enter the password for this account. This is a security measure to prevent anyone from changing this setting who does not already know the password.

That’s it! You’ve now configured your Windows 10 computer to not bother you with a password screen every time you reboot or switch users.
Security Concerns When Bypassing the Windows 10 Sign-in Screen

You should be aware of the security implications of bypassing the login screen. It obviously reduces the security of the account but by how much? Well, it’s important to realize that only people actually sitting down at the computer get to bypass the login. Anyone trying to remotely access your computer still has to know the password. There are really two main things to think about when deciding whether or not to do this bypass.
First, is your computer vulnerable to being physically compromised? If you have a laptop that you regularly take to school or work, and routinely leave unattended for short periods of time, then it seems fairly clear that bypassing the login would significantly damage your safety.
Conversely, if you have a home office located in the locked basement of your isolated mountaintop home, secured with laser perimeter fences and attack dogs, your machine is relatively physically secure, and you can probably do without the extra protection of a login screen. Though if you’re living in such a home, chances are you’re not the sort who would be considering turning off the login screen in the first place.
Second, do you share access to the machine with other people or are there others in your household who might use your computer when you’re not around? If you have children, a significant other, or roommates who use the same computer as you do at different times, then leaving your login process unsecured like this is a bad idea.

Your kids can accidentally switch over to your user account, and turn your desktop into a mess just by fooling around. Adult friends or roommates are less likely to completely mess up your configuration (though you’d be surprised by how careless some people are) but may be tempted to go snooping in your private folders or to play whimsical tricks like renaming every file on your desktop to “Pirated Pr0n Videos” just to prank you.
There are some common-sense steps you can take to increase your security without having the burden of memorizing yet another password.
Adding Security to Appropriate Areas

Whether or not you bypass the Windows 10 login screen, it would be wise to add appropriate levels of security to the parts of your computer that are most vulnerable or most important.
In determining where you need security functions and how extensive they should be, security experts recommend looking at the combination of the importance of a data loss in an area and the odds of the data loss occurring in the first place.
That is if you have two areas of potential data loss, either of which would be catastrophic, but one of the areas is of a type where a data loss could practically never happen, and the other is of a type where a data loss is quite possible, you should put much more security in the second area than in the first.
The consequences of a loss would be the same in either place, but it is only in the second area where you are actually likely to run into a problem.
Encryption for Privacy and Security
One simple way to protect information on your computer is by encrypting folders or files that contain sensitive information. For example, folders containing your tax returns or investment/financial information are a good choice for encryption.
Encrypting a directory is extremely fast, and working with encrypted files basically just involves typing in a password once in a while. Even consumer-grade encryption is basically impossible for a private party to break, requiring absurdly high amounts of time with a powerful supercomputer. Higher-grade encryption can protect your data from just about anyone.
Windows offers a set of highly functional, if bare-bones, built-in encryption tools. Alternatively, there are many high-quality free or premium commercial encryption utilities. We have a complete introduction to encryption that will get you up to speed on the topic if it’s new for you. It’s important for computer users to have a basic understanding of encryption and how it can help with security and privacy.
Virtual Private Networks (VPNs)
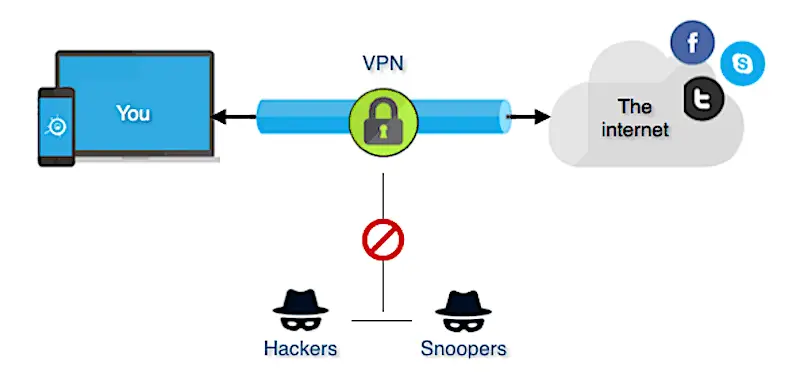
A virtual private network (VPN) is a method of extending a private network over the public Internet, enabling you to send and receive data as though you were on the same local network. VPNs are almost always encrypted offering a measure of security and privacy.
Companies typically provide VPNs to remote workers so they can have secure access to the same files, data, and software tools that they can access at the office. VPNs are not restricted to the rich and powerful, however – today’s VPN providers are available to anyone and can even be free.
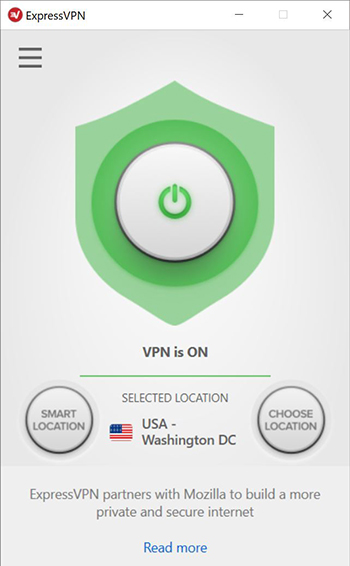
Installing a VPN is a good idea for anyone who uses the Internet, but is an absolutely essential task if you are using the Internet to download torrented software, movies, TV shows, or music. The VPN breaks the ability of your ISP to connect the file(s) being torrented with your physical computer, and are thus unable to file DCMA notices or cooperate with criminal prosecutions.
A VPN is a service provided by a company, rather than a piece of software that runs strictly on your computer. (Although many VPNs also have a client program that you do run on your computer, or even a physical router, making things a little complicated.) There are many VPN companies out there, with different features and pricing. We have a review of the best VPN providers, along with the best VPNs for security, and of course a guide to installing your VPN client on Windows 10.
Password Management for Convenience and Security
We highly recommended that you use a password manager so you don’t have to remember passwords and you’re not tempted to use the same password across multiple accounts. If you use the same password across accounts then if one account gets hacked, then multiple accounts can be hacked.
Also, password managers actually make it easier to log into accounts because the password manager makes it easy. With a password manager, you don’t even have to know what your passwords are or type them in manually. It makes life online a lot easier as well as secure – and you no longer have to rely on your insecure physical password book.
As I talked about in the introduction to this article, you have a lot of passwords in your life, for everything from personal finance to your kids’ movie channel subscriptions.

Passwords are supposed to increase security, but they often end up compromising it. Being human, we tend to use the same passwords for everything, which means that once a hacker has compromised one of them, they can usually get into all (or at least a lot) of your other accounts.
To make things worse, if we don’t use the same passwords for everything, most of us keep a piece of paper somewhere in our office with all the passwords written down. Handy for us, and of course even handier for the lucky burglar/hacker who decides to compromise our computer systems.

A password manager is a program that runs on your computer, or as a service on a website, that keeps track of your passwords for you without having to use ‘momsdiner1298’ for everything or putting everything in your life on a Post-It note on your monitor. There are a variety of great services out there. We have an overview of how passwords managers work along with recommendations for some, and an article on why you should use a password manager in the first place.
Have any other security and privacy tips to share with the community? Do you think it’s too risky to turn off the login password on your computer? Why or why not? Please let us know what you think in the comments below!