New Phishing Scam is Hosted by Google via Google Drive Exploit
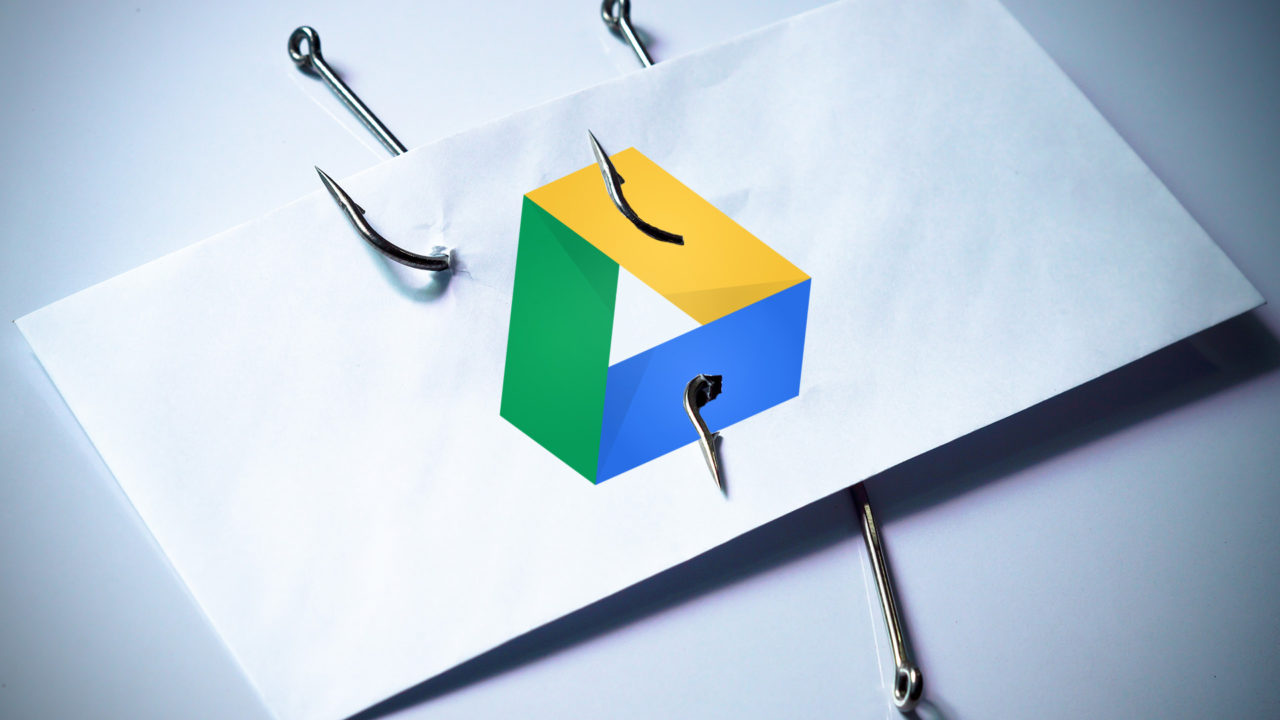
Phishing scams are nothing new, but a recent scam discovered by researchers at Symantec has caught the attention of the security industry. This new scam that targets Google Docs and Google Drive users is particularly effective because it uses Google’s own servers to host the malicious phishing website, making it difficult for users to detect that something has gone awry.
Most sophisticated phishing scams can recreate legitimate websites, such as a bank or online service, down to exacting detail. But these scams usually have one flaw, in that they’re not hosted by the “real” site or service, allowing users to see a fraudulent Web address in their browser or a lack of SSL security. But this new scam discovered by Symantec is unwittingly hosted by Google itself, giving victims an SSL-enabled Google address in their browsers.
Here’s how it works: the scammers created a folder inside a Google Drive account and marked it as public, allowing anyone to see it. They then upload a file to that folder, formatted to look like a Google log-in page, and used Google Drive’s Preview feature to get a publicly accessible URL for the file.
Scammers can then distribute this link via any method, tricking users into believing that it leads to a Google Docs file, and users who click on it will land on a page that looks like a Google log-in. While the URL won’t be the correct one for logging in to Google, it will show a Google.com domain and SSL security, which may be enough to trick most victims.
Users who enter their log-in credentials will have them recorded by the scammers via a PHP script and, perhaps worst of all, users who “log-in” will then be transferred to a real Google Doc file, making it likely that most victims won’t even realize they’ve been scammed until it’s too late.
Due to Google’s ever increasing range of services, scammers with a user’s Google login credentials will have access to email, calendars, documents, and even pay services like Google Music.
Despite the relative sophistication of this scam, users can still be protected by paying close attention to the address bar of a site before entering their login credentials, and by enabling two-factor authentication, which is strongly recommended for every service that offers it.