Should You Use a VPN with Popcorn Time? Yes!

TechJunkie’s coverage of VPNs has inspired quite a few email questions over the past couple weeks, some useful, some not so much. One of the more intriguing was ‘Why do I need to use a VPN with Popcorn Time?’ There are obvious security benefits of being able to use the internet without being identified and without the government or ISP spying on you but what about Popcorn Time in particular?
At the very least, your ISP won’t have much data on you to sell to third parties and at best, you could avoid prosecution for using programs such as Popcorn Time.
What is Popcorn Time?
Popcorn Time was originally designed as a program that allowed access to streamed media regardless of where you live. The original inventors were fed up with draconian licensing laws that said certain movies were only allowed to be viewed in certain countries at certain times.
The movie industry did, and still does, use an outdated model that seeks to control what we can see and when. Popcorn Time was originally designed to do away with that. That is a very laudable goal and one worthy of supporting, only the movie industry shut the original venture down.
As Popcorn Time was offered open source, other variations of the theme popped up across the internet. All with the same kind of design and intent.
The current range of Popcorn Time programs look and feel a lot like Netflix. They offer a web app with a list of movies and TV shows. Click on a movie and you have the option to stream and view there and then. It streams using Bit Torrent and plays in the app or your browser.
Why you need a VPN for Popcorn Time
Popcorn Time inhabits a legal gray area. The program itself and the bit torrent protocol are not illegal as they do not host or contain copyrighted material. Yet the predominant purpose of both is now the access of pirate content. Popcorn Time itself seems to have the sole purpose of allowing access to copyrighted material which does cause some legal issues.
The exact legal status of Popcorn Time depends on where in the world you live, but it is safe to assume it is likely illegal where you are. Or soon will be.
So the need to use a VPN with Popcorn Time should be obvious. If the program and the content you are streaming is likely illegal, you need to protect yourself. A VPN can help with that.
As part of their missions to control the movie industry, Hollywood and its cronies fund a range of outfits that actively police bit torrent websites and track illegal content online. On the face of it, you cannot blame them. After all, they paid for the movie to be made and deserve to be repaid for that investment right? If only it was that easy!
If you use bit torrent for anything other than completely legal means, it is safe to assume the torrent is being monitored. Private trackers are a little safer but still not foolproof as honeypots are sometimes used to trap downloaders.
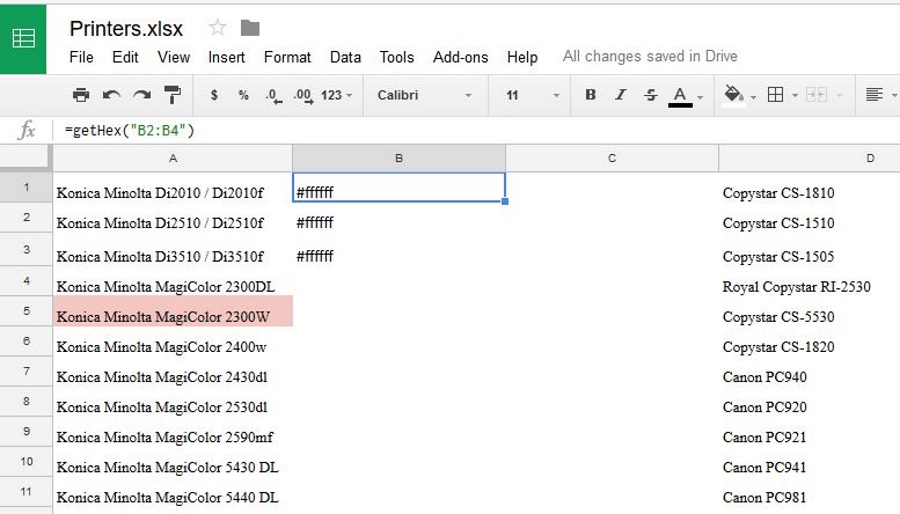
Even if isn’t actively monitored at that particular time, your ISP logs all your activity while online and has to keep those logs for a set amount of time (between 1 and 5 years depending on where you live). So even if your activity wasn’t picked up at the time, there is still a record of it later.
VPN avoids all that.

How a VPN helps protect Popcorn Time users
First, it is important to know that a VPN can help keep you anonymous but it isn’t foolproof. Connections can drop, DNS can leak and things can go wrong. What a VPN is, is the best form of defense we have right now.
A VPN wraps up your internet traffic in a secure encrypted package while online. The VPN software on your device creates a virtual tunnel to the VPN server run by the provider. Traffic between your computer and that server is encrypted and protected between those two points. Traffic is then decrypted and sent to its destination from that VPN server.
That means anyone watching a particular movie torrent will only see the VPN server IP address. They will only be able to back trace traffic back to the VPN server, not to your computer. Once traffic hits the VPN server, it is encrypted again and sent to your device.
While it sounds convoluted, the process runs very quickly. A good VPN provider will be able to maintain over 80 percent of your normal broadband speed when running a VPN.
If you would like to know more about how a VPN works, read ‘What is a VPN Tunnel and How Does it Protect Your Data?’ If you would like specific recommendations on what VPN to use with Popcorn Time, read ‘What Type of VPN is Best for Torrenting’.
Neither I, nor TechJunkie condones illegal activity but we do believe in the freedom of knowledge. Do with that knowledge what you will.















2 thoughts on “Should You Use a VPN with Popcorn Time? Yes!”
So how do I get around this??? Is there a button I missed orso???