How To Enable Windows Defender Guard For Microsoft Edge

Windows 10 users have been met with a huge problem as of late: increased malware and zero-day attacks. Malicious software like WannaCry and Petya are disastrous to computers, attempting identity theft, stealing files, and even destroying files so much that they’re not recoverable. Microsoft since then has increased Windows 10’s defenses against attacks like these, but as an extra layer of security, you might also want to consider using the Windows Defender Application Guard (WDAG).
Application Guard has been around for awhile, but only recently has it become available for Windows 10 Pro users. It was originally exclusive to Enterprise versions of Windows, but with this year’s Spring Creators Update, Windows 10 Pro users can add that extra layer of defense to their web browsing. Here’s how you can set it up.
How does Windows Defender Guard work?
There are a few requirements for you to even enable Application Guard. First, you need to have Windows 10 Pro. Secondly, you need to have a processor that supports virtualization, which many modern day CPUs do support. So, chances are, you can use Windows Defender Guard without a problem.
The way Windows Defender Guard works is by putting an application essentially in a sandbox. Viruses are allowed to get in the sandbox and might cause the program in the sandbox to become unstable, but malicious software isn’t able to reach outside of the sandbox. Once the sandbox is destroyed (i.e. when you close Microsoft Edge), everything in that sandbox disappears and your computer remains unharmed. You can reopen an application, which will restart that sandbox, but it restarts that sandbox with a clean slate, meaning you won’t have that virus there when you reopen the program. That’s the layman’s terms of what virtualization and Application Guard are and how they work. So, you can see how this would keep you safe from another zero-day attack like WannaCry and Petya.
How to enable Application Guard in Microsoft Edge
As you can see, Application Guard is almost necessary to have enabled on your computer. Luckily, it’s really easy to setup.
First, in the Search bar on your Windows task bar, search for Control Panel. Open the application.
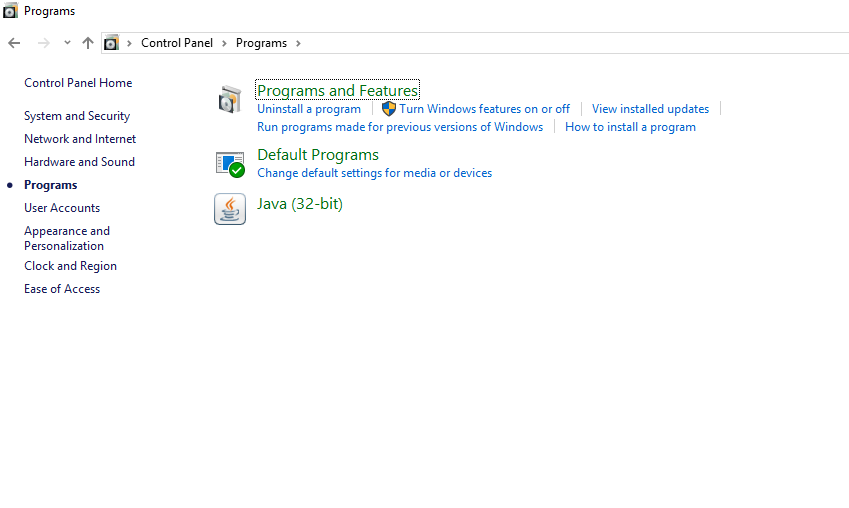
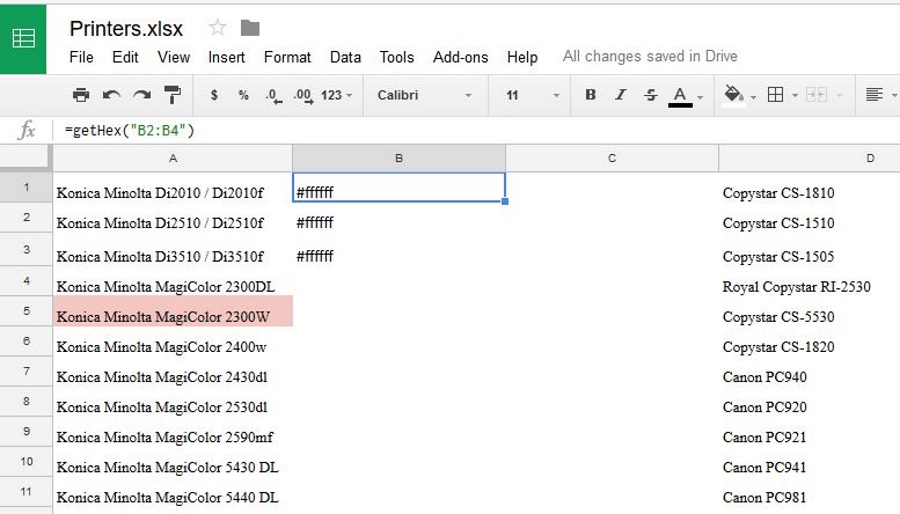
Next, select Programs, and under Programs and Features, click the Turn Windows features on or off link.
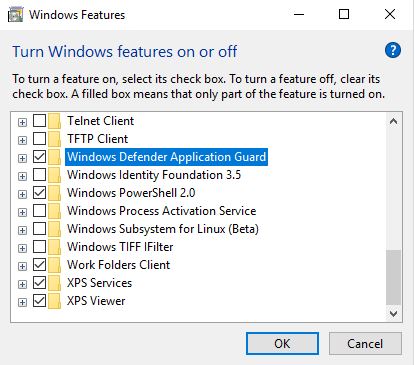
Now check the box for the Windows Defender Application Guard option. Press OK. If Windows won’t let you check the box, it’s likely that your hardware doesn’t support virtualization.
With the changes made, it’s best to restart your computer before continuing. It’s always a good practice to restart when you mess with anything that has to deal with virtualization and the like.
Once restarted, Application Guard is super simple to use in supported applications. Open up Microsoft Edge.
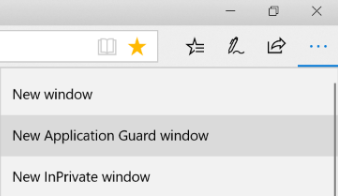
Click on the three-dot menu button, and select New Application Guard Window. Once you click that option, a new Microsoft Edge window is opened in a virtualized (i.e. isolated) environment outside of your computer. That’s that sandbox we talked about, which means you should be able to browse the web freely, without any viruses, malware, or zero-day software affecting your PC. And, if you run into trouble where you do find that you have a virus within your sandbox, it’s as simple as closing the window and starting a new one.
One neat thing that Application Guard allows you to do is that, because you’re in a sandbox or virtualized environment, you can freely browse untrusted sites without ruining your PC or putting your data at risk.
Closing
As you can see, it’s really easy to turn Application Guard on to start adding an extra layer of protection to your PC while browsing the Internet. You don’t have to use the Application Guard window all the time in Microsoft Edge, but it’s wise to do it when you’re browsing an untrusted site or a site that you might find questionable.